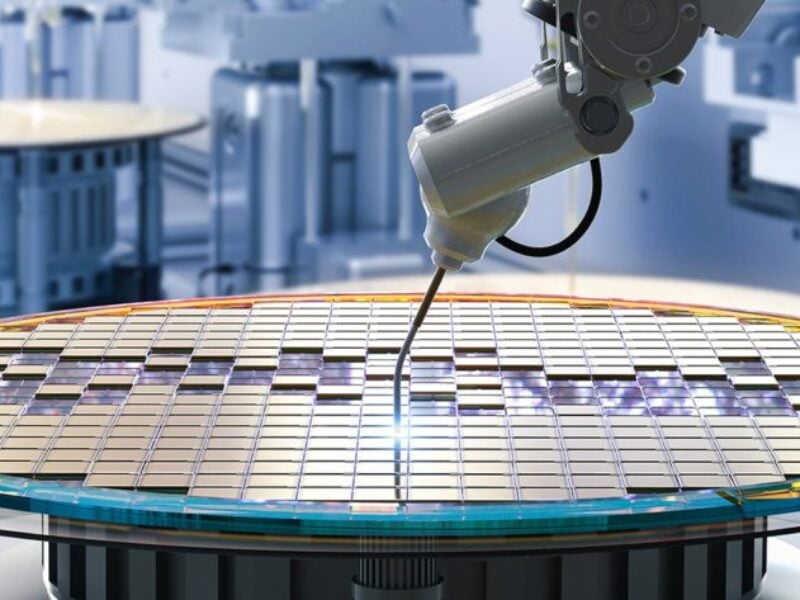
Using MRAM for more secure chips
 Cette publication existe aussi en Français
Cette publication existe aussi en Français
Researchers at Northwestern University in the US have developed a method that could allow for design and production of more secure semiconductor chips using magnetic memory.
They developed a voltage-controlled magnetic random-access memory (MRAM) technology, adding additional features that provide a unique fingerprint for each device and can be dynamically changed or adjusted to enhance security and protect against unauthorized cloning or copying.
The reconfigurable, physically unclonable functions (PUFs) can be used to secure the devices. Having a PUF that can be reconfigured by the chip’s end-user is beneficial because it allows the user to generate a new set of unclonable challenge-response pairs (CRPs) even if the initial CRPs have been fully or partially discovered.
- Deal to create quantum-secure edge processor
- Flex Logix and Intrinsic ID offer mission-critical eFPGA security
- IoT blockchain alliance promises security down to chip level
Khalili and his colleagues showed that the reconfiguration of their MRAM-based PUF can be realized quickly by very brief voltage pulses, representing a breakthrough for MRAM that could potentially make it more suitable for the application.
“There are significant security challenges resulting from the consolidation of the semiconductor manufacturing supply chain,” said Pedram Khalili, associate professor of electrical and computer engineering at the McCormick School of Engineering. “As a result, cryptographic technology based on hardware-level security primitives is emerging as an appealing option, with a key example being physically unclonable functions.”
“The performance of the proposed PUF was evaluated in terms of uniformity, uniqueness, reconfigurability, and reliability, achieving the required metrics in all areas,” said Khalili. “Our results provide a reliable and compact solution for hardware authentication in advanced integrated circuits with embedded MRAM, with applications in virtually all areas where hardware authentication matters, including automotive, aerospace, and financial infrastructure, among many others.”
www.mccormick.northwestern.edu/
 If you enjoyed this article, you will like the following ones: don't miss them by subscribing to :
eeNews on Google News
If you enjoyed this article, you will like the following ones: don't miss them by subscribing to :
eeNews on Google News





